In this article
- M2M communication protocols let devices talk to each other without human help. They form the backbone of IoT networks and industrial automation systems
- Application layer protocols like MQTT and CoAP make data exchange better for IoT devices with limited power and bandwidth
- Wireless protocols like cellular, Wi-Fi, and low power wide area networks connect IoT devices in different ways
- Choosing the right protocol depends on how big your system is, security needs, real-time performance, and power limits
- Different protocols need to work together for complete IoT system integration
- Understanding protocol features helps optimize IoT deployments for specific uses from smart homes to industrial networks
M2M communication protocols form the foundation of modern IoT systems. They let billions of devices talk to each other without human help. This guide looks at the key protocols that power machine-to-machine communication across industries. This includes smart home automation and industrial IoT networks. Understanding these communication technologies is vital for picking the right protocol for your IoT application.
IoT protocols have grown to handle different needs. These include power consumption limits, scalability needs, security protocols, and real-time data transmission. Each protocol serves specific use cases. Some work for lightweight sensor networks. Others work for complex industrial automation systems that need strong reliability.
This guide analyzes the most important m2m communication protocols. We compare their strengths, limits, and best applications. This helps you make smart decisions for your IoT projects.
- Understanding M2M Communication Protocols
- Application Layer Protocols for IoT
- Wireless Connectivity Protocols
- Protocol Selection Factors
- Security Protocols and Considerations
- Real-World IoT Applications
- Future Trends in M2M Communication
- Frequently Asked Questions
Understanding M2M Communication Protocols
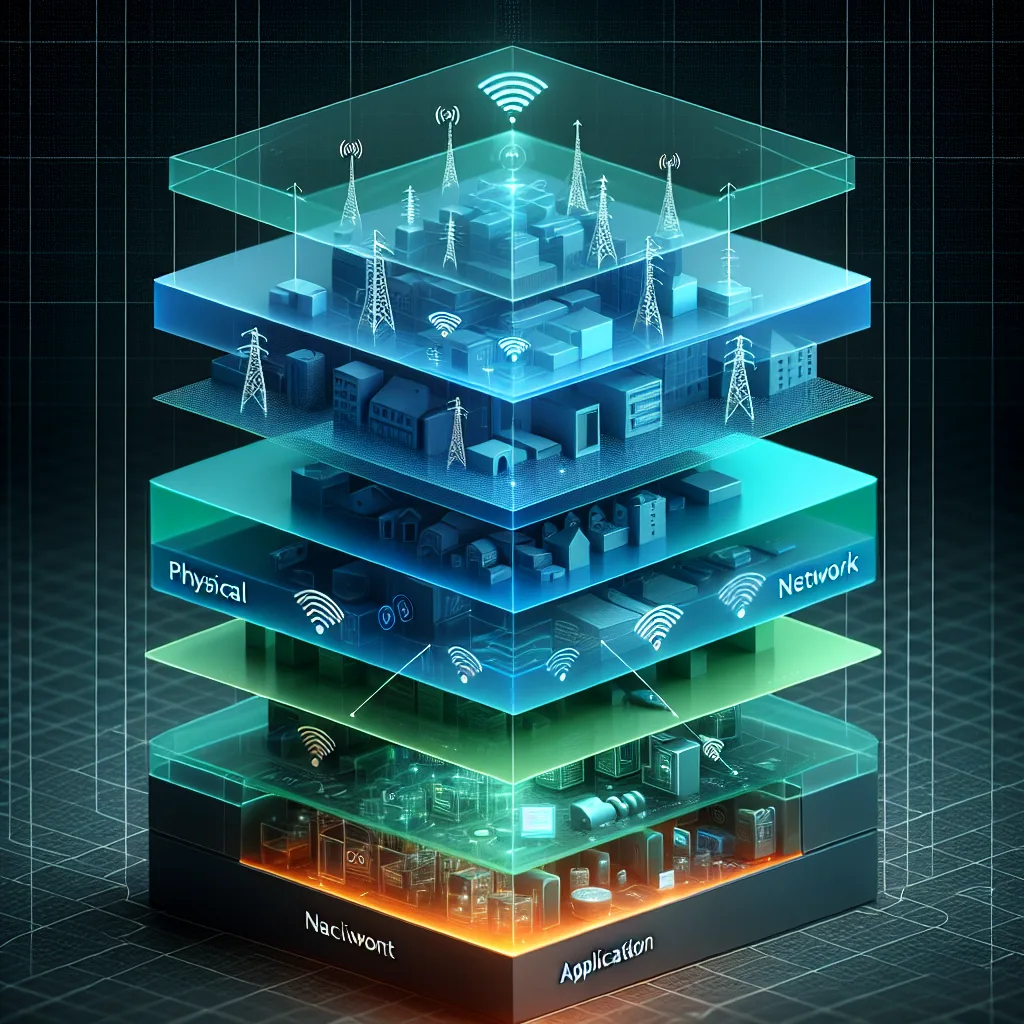
M2M communication protocols set the rules for how IoT devices share data without human help. These protocols create standards for transmission between sensors, controllers, gateways, and cloud platforms in an IoT network. The protocol structure typically covers multiple layers. This goes from physical connectivity to application-specific data formats.
IoT systems rely on these communication protocols to enable smooth data exchange between millions of connected devices. Each protocol handles specific challenges. These include bandwidth limits, power consumption needs, and reliable transmission in different environments. Modern IoT systems often use multiple protocols to handle different parts of device communication and data management.
Protocol Categories and Functions
IoT protocols fall into several functional groups. Application protocols handle high-level data formatting and messaging between IoT devices and applications. Layer protocols manage different parts of network communication. This goes from physical transmission to data presentation. Communication technologies include the basic methods that let devices communicate across networks.
Each category serves different purposes in the IoT ecosystem. Application layer protocols like MQTT optimize message delivery for devices with limited resources. Network layer protocols ensure proper routing and addressing. Understanding these differences helps in selecting appropriate protocols for specific IoT applications.
Application Layer Protocols for IoT
Application protocols form the top layer of IoT communication stacks. They define how IoT devices format and exchange data. These protocols work well with limited devices that have small processing power, memory, and battery life. The most important application protocols include MQTT, CoAP, and AMQP. Each offers unique benefits for different IoT use cases.
MQTT Protocol
MQTT (Message Queuing Telemetry Transport) is a lightweight publish-subscribe protocol. It works well for IoT device communication. This protocol excels when you need low power consumption and minimal bandwidth usage. MQTT operates on a broker-based system. IoT devices publish data to topics. Other devices or applications can subscribe to receive updates.
The protocol's efficiency makes it ideal for sensor networks. These devices must operate on battery power for long periods. MQTT supports quality of service levels. This ensures reliable message delivery even when networks are unstable. Its small code size allows use on microcontrollers with limited resources. This makes it popular for industrial IoT and smart home applications.
CoAP Protocol
CoAP (Constrained Application Protocol) is designed for resource-limited IoT devices. These operate in networks with data loss. This protocol uses a REST-based architecture similar to HTTP. But it's optimized for devices with limited processing power and spotty connectivity. CoAP enables direct device-to-device communication without needing a central broker.
The constrained application protocol supports both reliable and unreliable transmission modes. This lets developers balance reliability needs with power consumption. CoAP's built-in discovery features help IoT devices find and interact with nearby services automatically. This protocol works particularly well in mesh network deployments. Here, devices need to communicate directly with neighboring nodes.
Additional Application Protocols
AMQP (Advanced Message Queuing Protocol) provides enterprise-grade messaging for IoT applications. It works when you need guaranteed delivery and complex routing scenarios. XMPP, the extensible messaging and presence protocol, offers real-time communication with built-in presence information. This makes it suitable for collaborative IoT applications.
WebSocket protocols enable full-duplex communication over HTTP connections. This provides an efficient way to connect IoT devices with web applications. These application protocols often work together in comprehensive IoT systems. They handle different types of data exchange and communication needs.
Wireless Connectivity Protocols
Wireless protocols provide the physical and network layer foundation for IoT connectivity. They enable devices to communicate across various distances and network layouts. These protocols determine how data is transmitted through wireless networks. This covers short-range personal area networks to long-range wide area coverage.
Cellular IoT Protocols
Cellular protocols including NB-IoT (Narrowband IoT) and LTE-M provide wide area coverage for IoT devices. These need to communicate over long distances. These low power wide area network protocols are optimized for IoT applications. They need minimal power consumption while maintaining reliable connectivity across urban and rural environments.
NB-IoT excels in applications requiring deep indoor penetration and extended battery life. Examples include smart metering and asset tracking. LTE-M supports higher data rates and mobility. This makes it suitable for applications like connected vehicles and mobile sensor platforms. Both protocols support massive device deployments. They can handle thousands of IoT devices per cell tower.
Short-Range Wireless Protocols
Wi-Fi remains important for IoT devices that need high bandwidth. It works well in environments with existing wireless network infrastructure. The protocol offers excellent performance for applications like security cameras and multimedia devices. But it consumes more power than specialized IoT protocols.
Zigbee and Thread protocols create mesh networks. These allow IoT devices to extend network coverage by relaying data through neighboring devices. These protocols work particularly well in smart home automation. Here, devices need to communicate reliably throughout a building while maintaining low power consumption.
Bluetooth Low Energy (BLE) provides short-range connectivity with minimal power needs. This makes it ideal for wearable devices, health sensors, and proximity-based applications. The protocol's ability to operate on coin cell batteries for months makes it attractive for consumer IoT products.
Protocol Selection Factors
Selecting the right IoT protocol needs careful evaluation of multiple factors. These include power consumption needs, scalability requirements, security considerations, and application-specific performance needs. Each protocol offers different trade-offs. These must align with your IoT deployment goals and constraints.
Power and Resource Constraints
Power consumption is often the primary limit for battery-powered IoT devices. These must operate for years without maintenance. Protocols like MQTT and CoAP are specifically designed to minimize energy usage. They use efficient message formats and communication patterns. Low power protocols reduce transmission frequency and optimize sleep modes to extend battery life.
Memory and processing limitations also influence protocol selection. Limited devices need protocols with small code sizes. These can run on microcontrollers with limited RAM and storage. The protocol's complexity directly impacts the device's ability to implement other application features.
Scalability and Network Architecture
Scalability becomes critical when deploying thousands or millions of IoT devices in a single network. Some protocols handle large-scale deployments better than others. They use efficient addressing schemes, message routing, and bandwidth utilization. Protocols that support hierarchical network structures can better manage traffic in complex IoT systems.
Network topology requirements also influence protocol choice. Star topologies work well with broker-based protocols like MQTT. Mesh networks need protocols that support multi-hop routing and dynamic path discovery. The ability to handle network failures and automatically reconfigure connections is essential for maintaining reliability in large IoT deployments.
Real-Time Performance Requirements
Real-time applications need protocols that can guarantee low latency and predictable response times. Industrial automation systems often need millisecond-level response times. Some IoT protocols may not achieve this. The protocol's message overhead, routing complexity, and error handling all impact real-time performance.
Quality of service features help ensure critical messages receive priority treatment in busy networks. Protocols that support different service levels allow IoT systems to optimize performance for various types of data. This ranges from routine sensor readings to emergency alerts requiring immediate attention.
Security Protocols and Considerations
Security is a fundamental concern in IoT protocol selection. Connected devices often handle sensitive data and control critical systems. Modern IoT protocols must implement strong security measures. These include encryption, authentication, and access control to protect against various cyber threats.
Many IoT devices have limited computing resources. This restricts the complexity of security protocols they can implement. Lightweight cryptographic algorithms and efficient key management systems are essential. They maintain security without overwhelming device capabilities. The balance between security strength and resource consumption requires careful protocol evaluation.
Encryption and Authentication
End-to-end encryption ensures data remains protected throughout transmission from IoT devices to cloud platforms. Protocols like MQTT support TLS encryption to secure message content. CoAP implements DTLS for connectionless security. Authentication mechanisms verify device identity and prevent unauthorized access to IoT networks.
Certificate-based authentication provides strong security. But it requires proper certificate management across large IoT deployments. Pre-shared key systems offer simpler implementation but require secure key distribution and management processes. The chosen authentication method must scale appropriately with the IoT system size and security requirements.
Real-World IoT Applications

Different IoT applications have distinct protocol requirements. These are based on their operating environments, performance needs, and deployment constraints. Understanding how protocols perform in real-world scenarios helps guide selection decisions and optimization strategies for specific use cases.
Industrial IoT Networks
Industrial IoT applications need protocols that support real-time monitoring, predictive maintenance, and automation control. These environments often demand high reliability, predictable performance, and the ability to integrate with existing industrial systems. Protocols must handle harsh operating conditions. This includes electromagnetic interference and extreme temperatures.
Sensor networks in manufacturing facilities use protocols that can gather data from hundreds of measurement points. They maintain precise timing synchronization. The ability to prioritize critical alarms and control messages ensures safety systems can respond quickly to potentially dangerous conditions.
Smart Home and Building Automation
Smart home applications prioritize ease of installation, compatibility between different device manufacturers, and user-friendly management interfaces. Protocols must support automatic device discovery and configuration. This minimizes technical expertise requirements for end users.
Building automation systems need protocols that can integrate HVAC controls, lighting systems, security devices, and energy management platforms. The protocol for communication must support both scheduled operations and responsive control. This is based on occupancy patterns and environmental conditions.
Healthcare and Wearable Devices
Healthcare IoT applications need protocols that ensure patient data privacy, support real-time vital sign monitoring, and maintain reliable connectivity for critical health alerts. Low power consumption is essential for wearable devices. Patients must wear these continuously for extended monitoring periods.
Medical sensor networks must comply with healthcare data regulations. They also provide accurate, timely information to healthcare providers. Protocols must support both routine data collection and emergency alerting capabilities. These can trigger immediate medical response when needed.
Future Trends in M2M Communication
The evolution of m2m communication protocols continues as IoT deployments grow in scale and complexity. Emerging technologies including 5G networks, edge computing, and artificial intelligence integration are driving new protocol requirements and capabilities.
Edge computing reduces latency by processing data closer to IoT devices. This requires protocols that can efficiently distribute intelligence across network edges. This trend demands protocols that support local decision-making while maintaining connectivity to central management systems for coordination and updates.
Protocol Standardization and Interoperability
Increased focus on compatibility is driving convergence toward common protocol standards. These enable seamless communication between devices from different manufacturers. Standard protocols reduce integration complexity and support more flexible IoT system architectures.
The development of protocol translation gateways and middleware platforms helps bridge compatibility gaps between different IoT protocols. These solutions enable organizations to optimize protocol selection for specific device requirements. They maintain system-wide compatibility and data exchange capabilities.
Wireless Communication Technologies in M2M Networks
Wireless communication technologies form the backbone of modern m2m networks. They enable seamless data exchange between devices across vast distances. M2M communication enables autonomous data transmission without requiring human intervention. This allows industrial sensors to report status updates, smart meters to transmit usage data, and fleet vehicles to share location information in real-time. The right iot protocols ensure reliable connectivity even in challenging environments where traditional protocols might fail.
M2M devices use various wireless communication methods. This depends on their specific requirements and deployment scenarios. Mobile communication standards like LTE-M and NB-IoT provide wide-area coverage for applications requiring low power consumption and extended battery life. These lightweight communication solutions enable devices without constant power sources to operate for years while maintaining consistent network connectivity.
Protocol Selection for Industrial M2M Applications
Industrial m2m applications demand robust protocols and standards. These can handle harsh operating conditions and critical data transmission requirements. Communication networks in manufacturing environments must support real-time monitoring of equipment status, predictive maintenance alerts, and automated quality control systems. M2M protocols like Modbus RTU and Profibus have proven their reliability in factory automation scenarios. Here, millisecond response times determine operational efficiency.
Communication between iot devices becomes increasingly complex as industrial systems integrate more sensors and actuators. This comprehensive guide to iot protocols helps engineers evaluate which protocols work most effectively in specific industrial contexts. IoT security protocols play a crucial role in protecting sensitive manufacturing data from cyber threats while maintaining the low-latency communication essential for automated production lines.
Both iot and m2m systems require careful protocol selection to balance performance, security, and power consumption requirements. Communication methods that work well in office environments may not perform adequately in industrial settings with electromagnetic interference and extreme temperatures. Iot and m2m applications continue to drive innovation in protocol development, pushing manufacturers to create more resilient and efficient communication standards.
Protocol Layer Architecture in M2M Systems
Understanding protocol layer architecture helps engineers select appropriate protocols in this layer of the communication stack. Transport layer protocols handle the reliable delivery of data between M2M devices. Application-layer protocols manage the actual message formatting and interpretation. Each layer serves distinct functions that collectively enable robust communication within industrial networks.
Smart grid communication shows how layered protocol architectures optimize power distribution networks. These systems need protocols with specific requirements for real-time monitoring, load balancing, and fault detection across thousands of connected devices. The combination of multiple protocol layers ensures that smart grid infrastructure maintains reliability while supporting advanced analytics and automated response systems.
Protocol Selection Criteria for M2M Applications
Engineers must evaluate protocols already deployed in their existing infrastructure when selecting new M2M solutions. Common protocols like MQTT, CoAP, and HTTP each offer different advantages. This depends on bandwidth constraints, power requirements, and latency specifications. The range of communication protocols available today provides flexibility for diverse industrial applications, from factory automation to environmental monitoring systems.
Direct communication between devices requires protocols such as HTTP for web-based interfaces or specialized protocols to address specific industry requirements. Bi-directional communication enables autonomous data exchange between sensors, controllers, and management systems. This doesn't require constant human oversight. This capability transforms traditional monitoring systems into intelligent networks that respond dynamically to changing conditions.
Data communication protocols must support devices without human intervention while maintaining security and reliability standards. Communication in IoT environments demands protocols that can operate efficiently across different protocols and network layouts. The protocols listed in comprehensive comparison guides help engineers understand which solutions best match their specific deployment requirements and performance objectives.
Key M2M applications require careful protocol evaluation to ensure optimal performance and scalability. Modern protocols enable communication between diverse device types. This ranges from simple sensors to complex industrial controllers. Organizations benefit from understanding how various protocols handle authentication, encryption, and message routing to make informed implementation decisions.
When evaluating message-oriented middleware solutions, AMQP is an open standard that delivers exceptional reliability for M2M communications. This protocol excels in scenarios requiring guaranteed message delivery. This makes it ideal for financial transactions, industrial automation, and supply chain management systems. AMQP's broker-based architecture ensures messages persist even during network interruptions. This provides the fault tolerance that mission-critical M2M applications demand.
The choice between lightweight and feature-rich protocols depends heavily on your deployment constraints and reliability requirements. Battery-powered sensors in remote locations typically benefit from minimalist protocols that preserve energy. Industrial control systems require robust protocols that handle complex routing and guaranteed delivery. Understanding these trade-offs helps engineers select protocols that balance resource consumption with operational reliability.
Security implementations vary dramatically across M2M protocols. Some offer built-in encryption while others rely on transport layer protection. Modern M2M deployments increasingly prioritize end-to-end security, especially in healthcare, automotive, and smart city applications where data integrity directly impacts safety. Protocol selection should align with your specific security requirements and compliance standards.
Protocol Performance in Edge Computing Environments
Edge computing environments present unique challenges for M2M protocol selection. This is particularly regarding latency sensitivity and local processing capabilities. Protocols optimized for edge deployment minimize round-trip communications by supporting local decision-making and data gathering. This approach reduces bandwidth consumption while improving response times for time-critical industrial processes.
Scalability Considerations for Large M2M Networks
Large-scale M2M networks need protocols that handle thousands of concurrent connections without degrading performance. Protocol overhead becomes critical when managing extensive device fleets. Inefficient protocols can overwhelm network infrastructure and increase operational costs. Smart protocol selection considers both current deployment size and anticipated growth patterns to ensure long-term viability.
Frequently Asked Questions
What are the most important factors when selecting an IoT protocol for my application?
The key factors include power consumption requirements for your IoT devices, how many devices you plan to deploy, security protocols necessary for data protection, and real-time performance requirements. Consider whether your devices need low power operation, what level of security is required, and whether you need real-time communication capabilities.
How do MQTT and CoAP protocols differ in their IoT applications?
MQTT uses a broker-based publish-subscribe model ideal for centralized IoT systems with reliable connectivity. CoAP enables direct device-to-device communication better suited for distributed sensor networks. MQTT excels in applications requiring guaranteed message delivery. CoAP works well in limited environments with spotty connectivity and low power consumption needs.
Which wireless protocol is best for industrial IoT deployments?
Industrial IoT applications often need protocols that support real-time communication, high reliability, and harsh environmental conditions. Cellular protocols like NB-IoT provide wide area coverage for remote monitoring. Mesh protocols like Zigbee work well for local sensor networks. The choice depends on your specific automation requirements, transmission distances, and power consumption constraints.
How do security protocols impact IoT device performance and battery life?
Security protocols add computational overhead and transmission bytes that increase power consumption in IoT devices. Lightweight cryptographic algorithms and efficient key management help minimize this impact. The security level must balance protection needs with device constraints. Stronger encryption requires more processing power but provides better data protection for sensitive IoT applications.
Can different IoT protocols work together in the same system?
Yes, comprehensive IoT systems often use multiple protocols to optimize different aspects of device communication and connectivity. Protocol gateways and middleware platforms enable compatibility between different communication technologies. This allows you to select the best protocol for each device type while maintaining system-wide data exchange and management capabilities.
What is the role of application layer protocols in IoT device communication?
Application layer protocols define how IoT devices format and exchange data at the highest level of the communication stack. These protocols handle message structure, routing, and delivery confirmation between devices and applications. They optimize data transmission for limited devices while enabling complex IoT applications to function reliably across various network conditions and connectivity scenarios.
What are the key differences between IoT and M2M communication protocols?
IoT and M2M protocols differ mainly in their scope and complexity. IoT protocols typically support more diverse device types and cloud integration capabilities. M2M protocols focus on direct device-to-device communication with minimal human intervention. IoT protocols generally offer more sophisticated data processing and analytics features. Both protocol families prioritize efficient data exchange between devices.
How do wireless communication technologies impact M2M protocol selection?
Wireless communication technologies directly influence which m2m protocols perform best in specific deployment scenarios. Protocols and standards must align with the underlying wireless infrastructure to ensure reliable connectivity and efficient power management. The choice between cellular, Wi-Fi, or proprietary wireless solutions determines which communication methods will deliver the best performance for particular m2m applications.
Which protocols work best for devices without constant power sources?
Lightweight communication protocols like LoRaWAN, Sigfox, and NB-IoT excel for devices without reliable power connections due to their ultra-low power consumption designs. Traditional protocols often consume too much energy for battery-powered applications. These specialized m2m protocols enable years of operation on a single battery while maintaining reliable wireless communication capabilities.
How do IoT security protocols protect M2M networks from cyber threats?
IoT security protocols implement multiple layers of protection including device authentication, data encryption, and secure key management to safeguard communication networks. These protocols work with existing m2m protocols to create secure tunnels for sensitive data transmission. Modern iot security protocols also include features like certificate-based authentication and over-the-air security updates to protect against evolving cyber threats.
Which transport layer protocols work best for industrial M2M applications?
TCP provides reliable bi-directional communication for applications requiring guaranteed data delivery. UDP offers lower latency for time-sensitive control systems. Key M2M implementations often combine both protocols to address different communication requirements within the same network infrastructure.
How do common protocols handle communication in IoT environments?
Protocols such as HTTP work well for web-based device management. MQTT and CoAP optimize data communication for resource-limited devices. These protocols already include built-in features for handling spotty connectivity and managing power consumption in battery-operated sensors.
What enables direct communication between M2M devices without human intervention?
Communication enables autonomous data exchange through standardized message formats and automated response mechanisms built into modern protocols. Devices without human intervention rely on pre-configured rules and protocol-specific authentication methods to establish secure connections and exchange critical operational data.
How does protocol selection affect the range of communication capabilities?
The range of communication depends heavily on choosing protocols with specific power, bandwidth, and latency characteristics that match deployment requirements. Protocols listed in technical specifications define maximum transmission distances, supported data rates, and network topology limitations that directly impact system design and performance across different protocols.
What makes AMQP suitable for enterprise M2M applications?
AMQP is an open standard specifically designed for reliable message queuing in distributed systems. This makes it excellent for enterprise M2M deployments. Its advanced features include message persistence, complex routing capabilities, and guaranteed delivery mechanisms that ensure critical business data reaches its destination. The protocol's broker-based architecture provides centralized management and monitoring capabilities essential for large-scale industrial operations.
How do I choose between connection-oriented and connectionless M2M protocols?
Connection-oriented protocols like TCP-based solutions provide reliable data delivery and ordered message sequences. This makes them ideal for applications requiring guaranteed communication. Connectionless protocols offer lower overhead and better performance in scenarios where occasional message loss is acceptable, such as periodic sensor readings. Your choice should depend on whether your M2M application prioritizes reliability or efficiency.
What security features should I prioritize when selecting M2M communication protocols?
Essential security features include end-to-end encryption, device authentication, and message integrity verification to protect against data breaches and unauthorized access. Many modern M2M protocols incorporate TLS/SSL support, certificate-based authentication, and payload encryption as standard features. Consider protocols that align with industry-specific security standards and compliance requirements for your particular use case.
How do bandwidth limitations affect M2M protocol selection?
Bandwidth-limited environments need protocols with minimal overhead and efficient data encoding to maximize throughput for actual payload data. Protocols designed for cellular or satellite communications often include compression algorithms and optimized header structures to reduce transmission costs. Evaluate your available bandwidth against protocol overhead to ensure efficient utilization of network resources.
Select M2M communication protocols that match your specific deployment requirements including power consumption, bandwidth limitations, security needs, and scalability objectives. This comprehensive analysis of protocol capabilities provides the foundation for successful IoT implementations that deliver reliable connectivity and optimal performance across diverse industrial and consumer applications.
Related Articles
How MQTT Brokers Work: Architecture and Best Practices
Message brokers function as the central communication hub in IoT architecture. They manage message routing between connected devices through a publish-s...
OPC UA for Industrial M2M Communication
Manufacturing operations need strong communication protocols. These protocols connect old systems with new IoT infrastructure. OPC UA for industrial m2m...
WebSocket vs MQTT vs CoAP: Choosing the Best Protocol
Selecting the right communication protocol can make or break your IoT project. Choosing between MQTT, CoAP, and real-time protocols means understanding ...
